Understanding Cyber Security Precautions
 The security over the Internet is something that has to be treated very carefully. Cyber crimes are increasing every day and this is a trend that has no sign of reduction, since internet users are increasing every day. When you start using internet, you enhance your online security by installing some antivirus. This is just a small step. Besides getting help from the software, you should also be able to recognize the threats that loom large when you access the Internet. The emails coming into your inbox are already filtered at certain extent. This work is done by the service provider’s own filtering algorithm. There are security holes in the Internet that are evident on many sites you enter.
The security over the Internet is something that has to be treated very carefully. Cyber crimes are increasing every day and this is a trend that has no sign of reduction, since internet users are increasing every day. When you start using internet, you enhance your online security by installing some antivirus. This is just a small step. Besides getting help from the software, you should also be able to recognize the threats that loom large when you access the Internet. The emails coming into your inbox are already filtered at certain extent. This work is done by the service provider’s own filtering algorithm. There are security holes in the Internet that are evident on many sites you enter.
But you must need to identify where you can venture safely. The firewall is something that can protect you from the dangers that can be overlooked. The browser is the first door through which any security breach can take place. A browser itself has a certain degree of security. Internet Explorer, Mozilla Firefox and Chrome are more secure browsers that are available to users.
However, Internet Explorer is installed with several security weaknesses that have other means of fixing. You must make sure that software you install on your system must be updated so that you will not be left behind without protection.
The freeware software that come with a security label is something that can help you overcome the security threats on the Internet. This is an important method to stay safe from threats. The firewall protection along with adware and spyware are some tools that can keep you out of threats. These are some basic ways that help you to keep the system safe and prevent data theft, keep your browsing safer.
Malicious software tends to cause damage to your computer and is something you should be very careful with. The email that arrives in your inbox should be filtered. You should still be careful and take precautions while reading unknown emails. The unknown emails may contain attachments that can contain anything that cannot be something you would like to download to your system. The viruses spread once they are opened on the system. So if you find any file on your running an e-mail you should with all respect be cautious and be 100% sure before you open and install it on your computer.
You should see the file extension that is downloaded on your system. The malware scanners have some useful tools that can help you avoid the threats. The entire online system security is solely the responsibility of the user and how he uses the systems and understand the threats that may affect the same. The basic patches are available over the internet and software, along with some tools that can let you keep threats at bay. But cybercrime is very large. The best tool for keeping your data safe is to interact with the internet in a surefire way and do not depend on any unknown content that can be more than detrimental to you and your system.
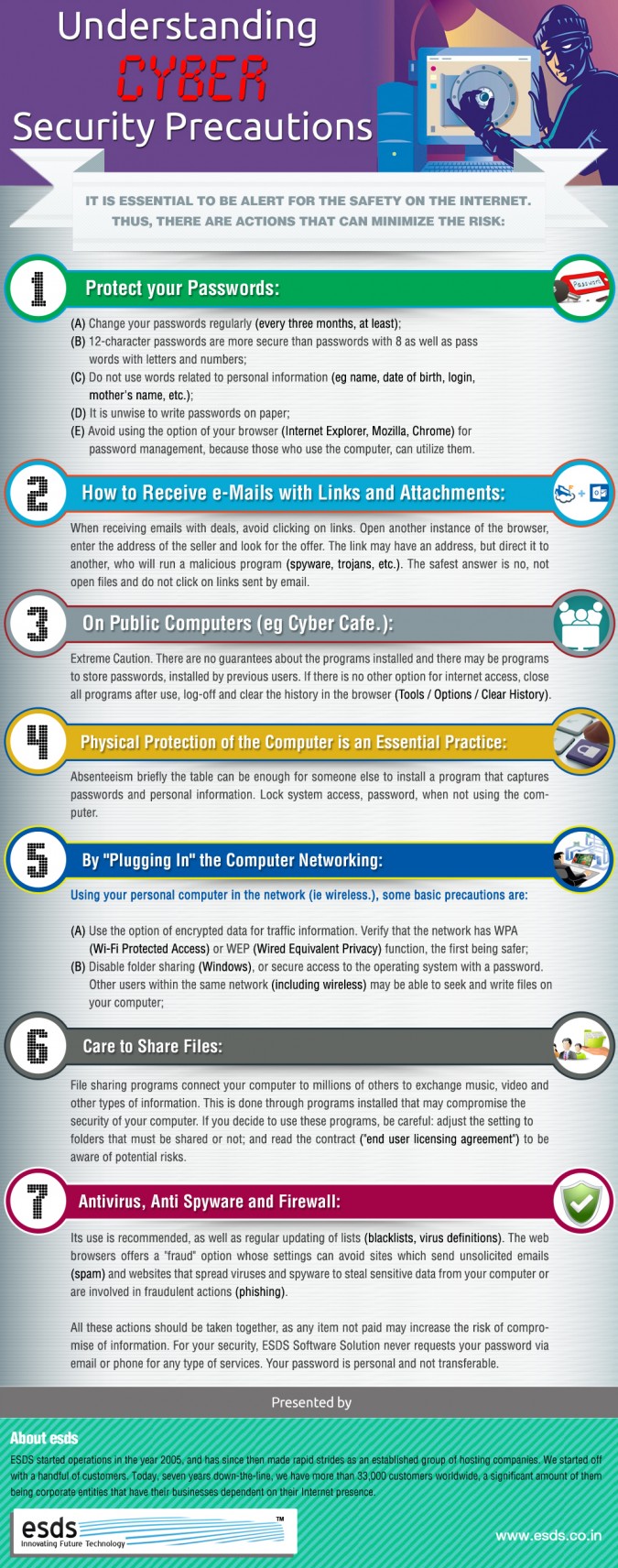
It is essential to be alert for the safety on the internet. Thus, there are actions that can minimize the risk:
• Protect Your Passwords:
- Change your passwords regularly (every three months, at least);
- 12-character passwords are more secure than passwords with 8 as well as passwords with letters and numbers;
- Do not use words related to personal information (eg name, date of birth, login, mother’s name, etc.);
- It is unwise to write passwords on paper;
- Avoid using the option of your browser (Internet Explorer, Mozilla, Chrome) for password management, because those who use the computer, can utilize them.
• How To Receive e-Mails With Links And Attachments:
When receiving emails with deals, avoid clicking on links. Open another instance of the browser, enter the address of the seller and look for the offer. The link may have an address, but direct it to another, who will run a malicious program (spyware, trojans, etc.). The safest answer is no, not open files and do not click on links sent by email.
• On Public Computers (eg Cyber Cafe.):
Extreme Caution. There are no guarantees about the programs installed and there may be programs to store passwords, installed by previous users. If there is no other option for internet access, close all programs after use, log-off and clear the history in the browser (Tools / Options / Clear History).
• Physical Protection Of The Computer Is An Essential Practice:
Absenteeism briefly the table can be enough for someone else to install a program that captures passwords and personal information. Lock system access, password, when not using the computer.
• By “Plugging” The Computer Networking:
Using your personal computer in the network (ie wireless.), some basic precautions are:
- Use the option of encrypted data for traffic information. Verify that the network has WPA (Wi-Fi Protected Access) or WEP (Wired Equivalent Privacy) function, the first being safer;
- Disable folder sharing (Windows), or secure access to the operating system with a password. Other users within the same network (including wireless) may be able to seek and write files on your computer;
• Care To Share Files:
File sharing programs connect your computer to millions of others to exchange music, video and other types of information. This is done through programs installed that may compromise the security of your computer. If you decide to use these programs, be careful: adjust the setting to folders that must be shared or not; and read the contract (“end user licensing agreement”) to be aware of potential risks.
• Antivirus, Antispyware And Firewall:
Its use is recommended, as well as regular updating of lists (blacklists, virus definitions). The web browsers offers a “fraud” option whose settings can avoid sites which send unsolicited emails (spam) and websites that spread viruses and spyware to steal sensitive data from your computer or are involved in fraudulent actions (phishing).
All these actions should be taken together, as any item not paid may increase the risk of compromise of information. For your security, ESDS Software Solution never requests your password via email or phone for any type of services. Your password is personal and not transferable.
- How Cloud Computing Is Changing The Labor Market - March 25, 2015
- Adopting Infrastructure as a Service Can be a Good Deal - March 17, 2015
- Will Virtualize? Take These Six Points Into Consideration - March 12, 2015
Yes its very important to be aware from cyber crime.Posted steps are excellent.
outstanding post.