Virtual Networks and Security Challenges
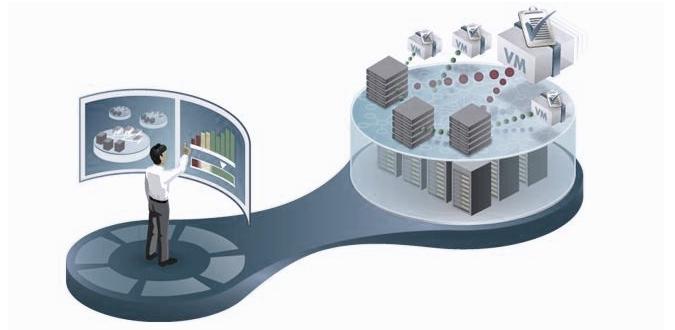
The sector recorded a real race for the virtualization of data centers and server hosting, in the wake of technological and economic advantages it can offer. The companies, however, should be conscious of the risk arising from plunging too quickly into cloud computing services, since virtual environments have many implications of compliance and safety.
Without doubt, virtualization creates an additional layer within the IT infrastructure, where often traditional security software, designed for physical environments, has a lack of visibility. This introduces vulnerabilities into the network, and visible gaps in the traffic between VMs. The new virtual machines that are installed automatically on the platform (especially in the case of an uncontrolled expansion of the VM) should be protected, regularly and systematically. The VMs are migrated from one physical platform to another – due to expansion of infrastructure or broken hardware – it also needs to be protected and monitored to avoid downtime during the live migration of VMs.
In addition to these internal threats, companies must protect their virtual environments also against external threats. Virtual environments can be even more dangerous than physical since the same techniques of attack and the same threats that exist in the physical layer exist in the virtual platform, where applications are not physically separated. This means that if a host server is under attack and the virtualization layer is compromised, this too can expose all the virtual machines to compromise on the infrastructure, all applications and data.
What are the best security practices for maintaining a secure virtual network?
The ideal solution must provide the same level of security present on the physical servers, virtual machines and applications:
First of all virtual machines too separate and protect the traffic between them, and hypervisor. The integration with it is important to ensure that the protection is running the hypervisor itself, not only on the virtual machine.
Secondly, the solution must proactively protect against external threats, with firewalls and intrusion prevention capabilities.
Third, to ensure unified management for both physical and virtual environments, making it easier for administrators to manage security.
It is important that the solution does all the above, without compromising the flexibility and scalability of the virtual system – security should help to exploit the benefits of virtualization, and not to mitigate them.
In addition, the solution must provide protection at all levels of security and not only at the network level. Of course, all levels of protection applied to the movement in the physical world, must also be implemented in the virtual environment.
Conclusion
Virtualization, as each new technology presents new risks for a company, incorrect implementation of security for a real environment may negatively impact on a company, exposing it to new risks and threats to security. For this reason, the implementation of the security architecture must be appropriate in a virtual environment, and knowledge of how to stay updated and protected against both internal and external threats, is a must for IT managers.
- How Cloud Computing Is Changing The Labor Market - March 25, 2015
- Adopting Infrastructure as a Service Can be a Good Deal - March 17, 2015
- Will Virtualize? Take These Six Points Into Consideration - March 12, 2015