Standards Of IT Security And The Providers Of The “Cloud”
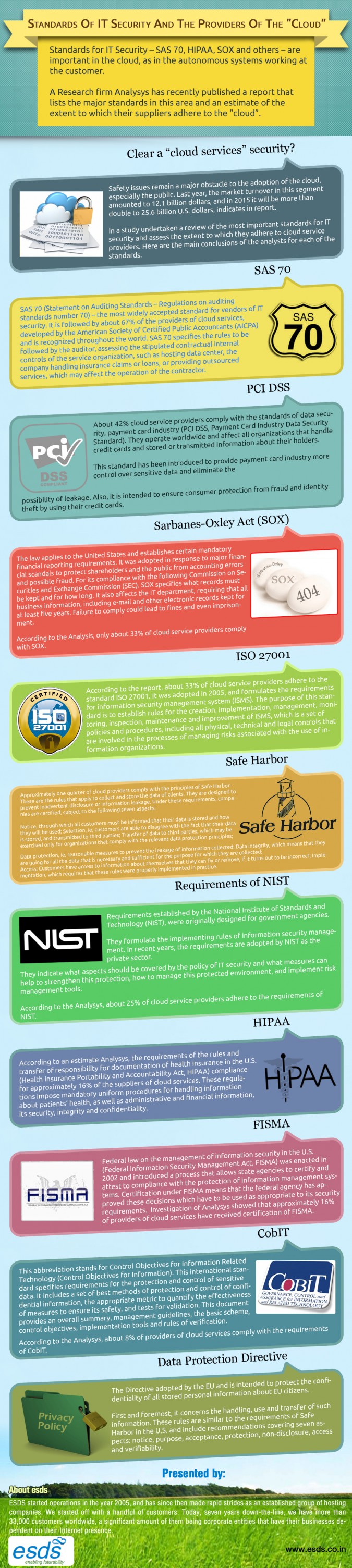 Standards for IT Security – SAS 70, HIPAA, SOX and others – are important in the cloud, as in the autonomous systems working at the customer. A Research firm Analysys has recently published a report that lists the major standards in this area and an estimate of the extent to which their suppliers adhere to the “cloud”.
Standards for IT Security – SAS 70, HIPAA, SOX and others – are important in the cloud, as in the autonomous systems working at the customer. A Research firm Analysys has recently published a report that lists the major standards in this area and an estimate of the extent to which their suppliers adhere to the “cloud”.
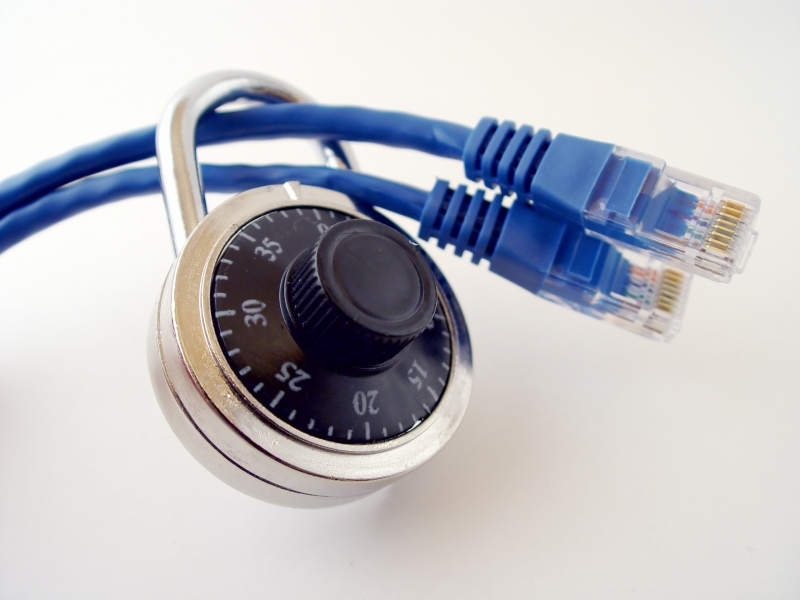
Clear a “cloud services” security?
Safety issues remain a major obstacle to the adoption of the cloud, especially the public. Last year, the market turnover in this segment amounted to 12.1 billion dollars, and in 2015 it will be more than double to 25.6 billion U.S. dollars, indicates in report.
In a study undertaken a review of the most important standards for IT security and assess the extent to which they adhere to cloud service providers. Here are the main conclusions of the analysts for each of the standards.
SAS 70
SAS 70 (Statement on Auditing Standards – Regulations on auditing standards number 70) – the most widely accepted standard for vendors of IT security. It is followed by about 67% of the providers of cloud services, developed by the American Society of Certified Public Accountants (AICPA) and is recognized throughout the world. SAS 70 specifies the rules to be followed by the auditor, assessing the stipulated contractual internal controls of the service organization, such as hosting data center, the company handling insurance claims or loans, or providing outsourced services, which may affect the operation of the contractor.
PCI DSS
About 42% cloud service providers comply with the standards of data security, payment card industry (PCI DSS, Payment Card Industry Data Security Standard). They operate worldwide and affect all organizations that handle credit cards and stored or transmitted information about their holders. This standard has been introduced to provide payment card industry more control over sensitive data and eliminate the possibility of leakage. Also, it is intended to ensure consumer protection from fraud and identity theft by using their credit cards.
Sarbanes-Oxley Act (SOX)
The law applies to the United States and establishes certain mandatory financial reporting requirements. It was adopted in response to major financial scandals to protect shareholders and the public from accounting errors and possible fraud. For its compliance with the following Commission on Securities and Exchange Commission (SEC). SOX specifies what records must be kept and for how long. It also affects the IT department, requiring that all business information, including e-mail and other electronic records kept for at least five years. Failure to comply could lead to fines and even imprisonment.
According to the Analysis, only about 33% of cloud service providers comply with SOX.
ISO 27001
According to the report, about 33% of cloud service providers adhere to the standard ISO 27001. It was adopted in 2005, and formulates the requirements for information security management system (ISMS). The purpose of this standard is to establish rules for the creation, implementation, management, monitoring, inspection, maintenance and improvement of ISMS, which is a set of policies and procedures, including all physical, technical and legal controls that are involved in the processes of managing risks associated with the use of information organizations.
Safe Harbor
Approximately one quarter of cloud providers comply with the principles of Safe Harbor. These are the rules that apply to collect and store the data of clients. They are designed to prevent inadvertent disclosure or information leakage. Under these requirements, companies are certified, subject to the following seven aspects:
- Notice, through which all customers must be informed that their data is stored and how they will be used;
- Selection, ie, customers are able to disagree with the fact that their data is stored, and transmitted to third parties;
- Transfer of data to third parties, which may be exercised only for organizations that comply with the relevant data protection principles;
- Data protection, ie, reasonable measures to prevent the leakage of information collected;
- Data integrity, which means that they are going for all the data that is necessary and sufficient for the purpose for which they are collected;
- Access: Customers have access to information about themselves that they can fix or remove, if it turns out to be incorrect;
- Implementation, which requires that these rules were properly implemented in practice.
Requirements of NIST
Requirements established by the National Institute of Standards and Technology (NIST), were originally designed for government agencies.
They formulate the implementing rules of information security management. In recent years, the requirements are adopted by NIST as the private sector. They indicate what aspects should be covered by the policy of IT security and what measures can help to strengthen this protection, how to manage this protected environment, and implement risk management tools.
According to the Analysys, about 25% of cloud service providers adhere to the requirements of NIST.
HIPAA
According to an estimate Analysys, the requirements of the rules and transfer of responsibility for documentation of health insurance in the U.S. (Health Insurance Portability and Accountability Act, HIPAA) compliance for approximately 16% of the suppliers of cloud services. These regulations impose mandatory uniform procedures for handling information about patients’ health, as well as administrative and financial information, its security, integrity and confidentiality.
FISMA
Federal law on the management of information security in the U.S. (Federal Information Security Management Act, FISMA) was enacted in 2002 and introduced a process that allows state agencies to certify and attest to compliance with the protection of information management systems.
Certification under FISMA means that the federal agency has approved these decisions which have to be used as appropriate to its security requirements.
Investigation of Analysys showed that approximately 16% of providers of cloud services have received certification of FISMA.
CobIT
This abbreviation stands for Control Objectives for Information Related Technology (Control Objectives for Information). This international standard specifies requirements for the protection and control of sensitive data. It includes a set of best methods of protection and control of confidential information, the appropriate metric to quantify the effectiveness of measures to ensure its safety, and tests for validation. This document provides an overall summary, management guidelines, the basic scheme, control objectives, implementation tools and rules of verification.
According to the Analysys, about 8% of providers of cloud services comply with the requirements of CobIT.
Data Protection Directive
The Directive adopted by the EU and is intended to protect the confidentiality of all stored personal information about EU citizens.
First and foremost, it concerns the handling, use and transfer of such information. These rules are similar to the requirements of Safe Harbor in the U.S. and include recommendations covering seven aspects: notice, purpose, acceptance, protection, non-disclosure, access and verifiability.
- How Cloud Computing Is Changing The Labor Market - March 25, 2015
- Adopting Infrastructure as a Service Can be a Good Deal - March 17, 2015
- Will Virtualize? Take These Six Points Into Consideration - March 12, 2015