How to Reduce Data Breach Risk and Eliminate Consequences
There will always be individuals and organizations dedicated to finding vulnerabilities in systems, looking to capitalize on weak areas. However, there are many different steps businesses can take to reduce their risk of a data breach and eliminate some of the more harmful consequences that come from being a victim of a breach.
How Do Data Breaches Happen?
According to IBM’s Cost of a Data Breach 2022 report, compromised or stolen credentials are the most frequent reason for a data breach. This attack vector is responsible for about one in five breaches. Phishing, improper cloud configuration, flaws in third-party software, and unethical insiders are additional frequent causes of data breaches.
Data breaches may also occur in organizations as a result of a breach in physical security, a system flaw, a compromise of business email, social engineering, or data or a device that is accidentally lost.
What Information is at Risk?
Data breaches can happen to any organization, regardless of size or industry. However, some types of data are more appealing to hackers than others, which raises the possibility of a breach.
Personally Identifiable Information
Personally identifiable information (PII) is any kind of data that can be associated with an identifiable person. Your license numbers, birth dates, social security numbers, email addresses, phone numbers, credit card numbers, and passwords connected to a user’s name, username, or other identifiers are examples of personal data.
Financial Details
Financial data is particularly susceptible to data breaches, especially when combined with personal information. Any financial data obtained through a data breach can be used for fraud or identity theft, allowing a bad actor to make unauthorized purchases or file reports in another person’s name.
Health Data
The frequent theft and compromise of health information may seem strange. However, for the past 12 years running, the healthcare sector has incurred the highest costs due to data breaches. In 2022, the average cost of a data breach in this sector was $10.10 million, while it cost $5.97 million on average in the financial sector. As with financial information, extremely private PII like social security numbers that can be used to commit identity theft can also be found in health information. Sometimes only one or two key pieces of information can be exposed in financial breaches. With regard to health information, a wider variety of PII is frequently accessible in one location.

Intellectual Property
The existence of valuable intellectual property within an organization may also serve as justification for a data breach. If sold to the right buyer, trade secrets, patents that are still in development, or other confidential information may be very valuable. Just over 10% of all data breaches are thought to be the result of insider actions, so malicious insiders may know someone who wants this information.
Competitor Intelligence
Similarly, information about competitions might be interesting to the right group of people. Certain information can be used to gain a competitive advantage, whether a business has information about its rivals or a rival is looking to learn more about a rival’s pricing or marketing tactics.
Legal Information
Legal records like contracts and agreements may be valuable, particularly for the private information they do hold. Similar to how financial and health information can be misused, data found in legal information can be used to commit fraud.
Information on IT security
In the same way that PII can let more sensitive information leak out as the cybercriminals put the pieces together, IT security data can do the same in an organization’s systems. Uncovering passwords or other crucial credentials can act as a keyhole, occasionally opening the door to entire systems.
How to Reduce Data Breach Risk and Eliminate Consequences?
To reduce the likelihood of a data breach, various tests and assessments can be used:
Several types of tests and assessments can be used to lower the risk of a data breach:
- Security audits can be used to verify that a company is adhering to security procedures and regulatory requirements.
- Before hackers do, vulnerability assessments can assist in identifying security holes in a company’s systems and networks.
- The goal in penetration testing is to identify security flaws in a system by having an ethical hacker attempt to use it against it.
- Employee training fosters a cybersecurity culture within an organization. Training can help businesses ingrain best practices. Regular tests can also be used to determine which employees would benefit from additional training.
Restrict Access
Most employees probably don’t require access to every aspect of your system. Access should be restricted so that only those who need it can access the most sensitive data, such as financial or health information, and other PII. Additional security measures include keycard access, two-factor authentication, computer timeouts after a set period of inactivity, and others.
Integrating Encryption
Data that has been encrypted cannot be accessed without a unique key. When stored on a physical device, data should be encrypted both in transit and at rest (when it is being transmitted over a network). When in use, it can also be encrypted (while data is being processed by a system). Increasing encryption will reduce the likelihood of a data breach.
Frequent Updates
It happens frequently that vulnerabilities result from recently found issues in a third-party tool. If your company doesn’t have a plan for routine patching and updating, this could leave gaps that could lead to data breaches. A system for identifying patches that are especially crucial should be in place, as well as a regular schedule for checking for and running updates.
Restoring Files
The time and resources required to get the business back up and running are some of the biggest costs associated with a data breach. This expense and the time required to restore data can be decreased by using a reliable backup and data recovery system. Systems can be restored in a matter of minutes with the highest levels of backup and recovery, with the least amount of data loss.
Constrained Access
Conditional access, which is similar to restricting access, conditional access implies restricting access for users based on particular circumstances, such as the time of day, the device they are using, or their location.
Security Guidelines
The security posture of an organization will continue to be strengthened by any new security policies. They may consist of the evaluations, encryption, and access control previously mentioned. They may also include firewalls, intrusion detection systems, and new password policies.
Getting Advice
It’s a good idea to seek outside assistance if you feel that your company lacks the internal expertise necessary to significantly reduce your risk of data breaches. The risk of a data breach can be reduced by consulting with and even assisting your organization in implementing best practices. Managed security providers and other cybersecurity experts can do this.
How Cyber Security Services Prevent Data Breaches?
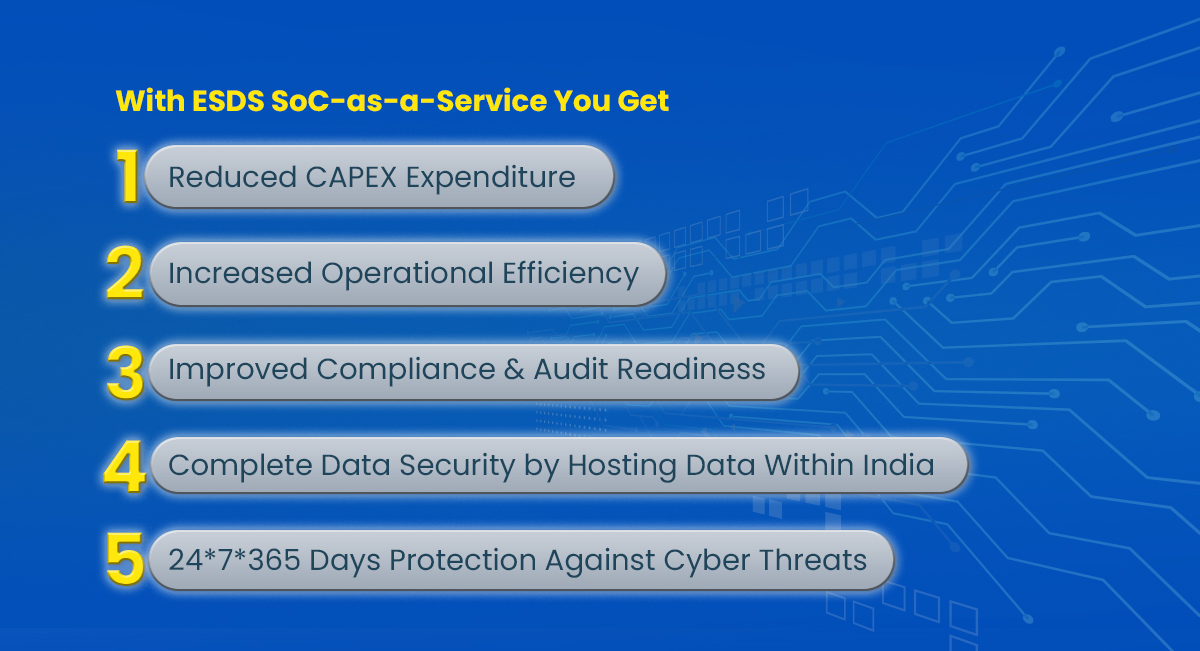
Threats can come from many sides. It’s easier to prevent a data breach by having a partner in your corner. In addition to implementing the aforementioned measures, organizations can further enhance their cybersecurity posture by leveraging comprehensive cybersecurity monitoring services. These services offer cutting-edge solutions that continuously monitor network traffic, system logs, and user activities to detect and respond to potential security threats in real-time. Advanced security analytics and threat intelligence capabilities enable proactive threat hunting and swift incident response. With round-the-clock monitoring and advanced threat detection technologies, businesses can gain valuable insights into their security landscape, identify vulnerabilities, and fortify their defenses. By partnering with experienced cybersecurity providers, organizations can benefit from a dedicated team of experts who provide proactive monitoring, threat mitigation, and incident management, ensuring robust protection against data breaches and cyberattacks.
At ESDS, we help you identify security flaws, detect advanced threats, and respond to them. Learn more about ESDS Cyber Security Services, by reaching out to us today. The holistic security solutions we provide answer your business’s safety concerns because your business deserves top-notch security!
Do you have what it takes to survive an attack on your own?
We’re listening! Tell us your thoughts in the comments.
- 6 Ways AI Reinvents the Security Landscape - January 9, 2024
- Top 6 Current Cybersecurity Trends For 2024 - January 9, 2024
- What Have We Learned from The Recent Cybersecurity Incidents? - January 3, 2024

