14 Consequences Your Business Might Face After a Data Breach
Data breaches are a growing issue which can be quite expensive. According to IBM, the average cost of a data breach reached a record high in 2022, reaching $4.35 million. Even worse, 83% of businesses have experienced multiple breaches, which can damage consumer confidence and result in irreparable revenue losses. We’ll talk about how data breaches happen, the types of data that are most frequently targeted, the repercussions that can follow a data breach, and how businesses can defend themselves from outside threats.
What Exactly is a Data Breach?
A data breach occurs when data without the permission or knowledge of the organization that owns the data is taken, accessed, altered, copied, or sent somewhere else. A data breach may be started by external threat actors like cybercriminals. It may also originate internally, either as a result of lax security measures, bad actors on the inside, or improper equipment disposal.
For businesses and organizations, a data breach can start as a small crack in the wall and grow quickly into a major problem.
14 Consequences of a Data Breach
Data breaches can cause both short-term and long-term consequences, affecting everyone from employees to partners to end users with any tangential connections. Here are some of the most severe consequences of a data breach for a business:
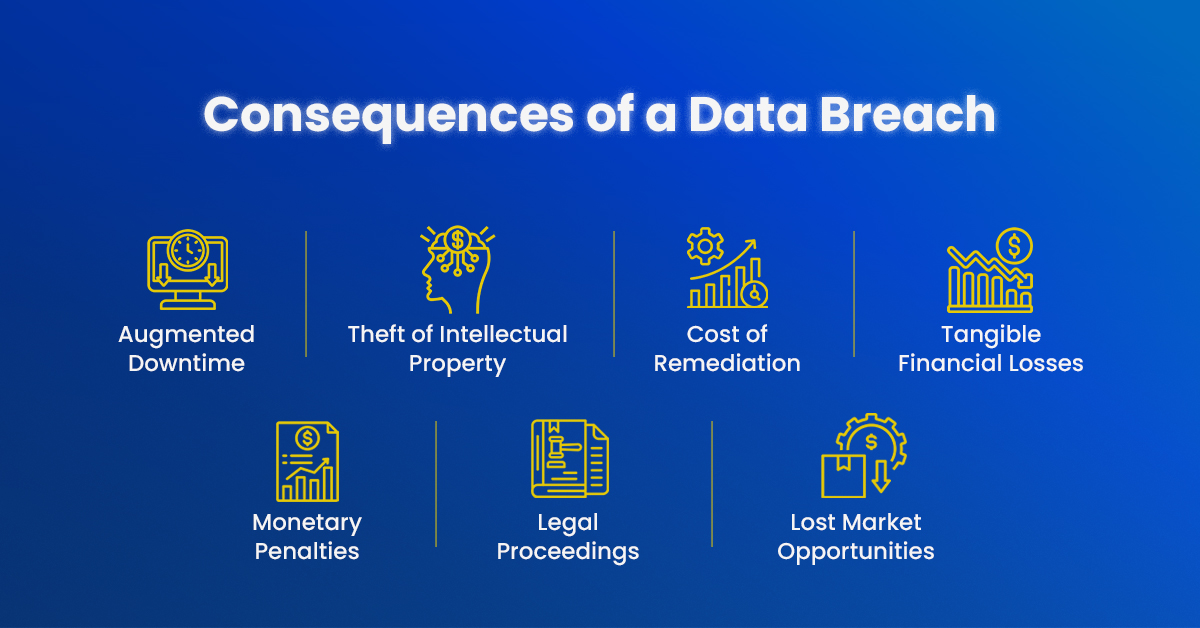
- Augmented Downtime: If data has been compromised and components of the system must be shut down in order to contain it, or worse, if the breach includes a ransomware attack in which data is being held hostage, this can result in increased downtime for a company. The second-highest share of a data breach’s cost is made up of lost revenue and business disruption, much of which can be attributed to downtime.
- Theft of Intellectual Property: Intellectual property theft can result in a competitor releasing a product that is currently in development to gain an edge, a counterfeit product hitting the market, or other harm to a company.
- Cost of Remediation: When a company experiences a data breach, the biggest cost is that of detection and escalation. Forensics and investigations, crisis management, evaluations and audits, and public relations campaigns are all remediation measures that, on average, cost a company $1.44 million. A business spends, on average, $1.18 million on post-breach responses, such as help desks, legal fees, fines from government agencies, product discounts, and more.
- Tangible Financial Losses: Downtime is a significant cause of direct financial loss because it reduces the revenue that would have been generated if a business could operate normally during that time.
- Legal Consequences and Monetary Penalties: Paying regulatory fines and penalties is a mandatory component of remediation following a breach. This can become an expensive endeavor for businesses if the security measures in place didn’t meet regulatory standards.
- Legal Proceedings and Claims: Conducting business in a non-compliant manner can expose an organization to legal action and damage claims. Businesses might be required to provide ongoing credit reporting services or compensate end users for compromised data.
- Lost Market Opportunities: Losing out on potential new business opportunities as a result of a data breach can also result in financial loss.
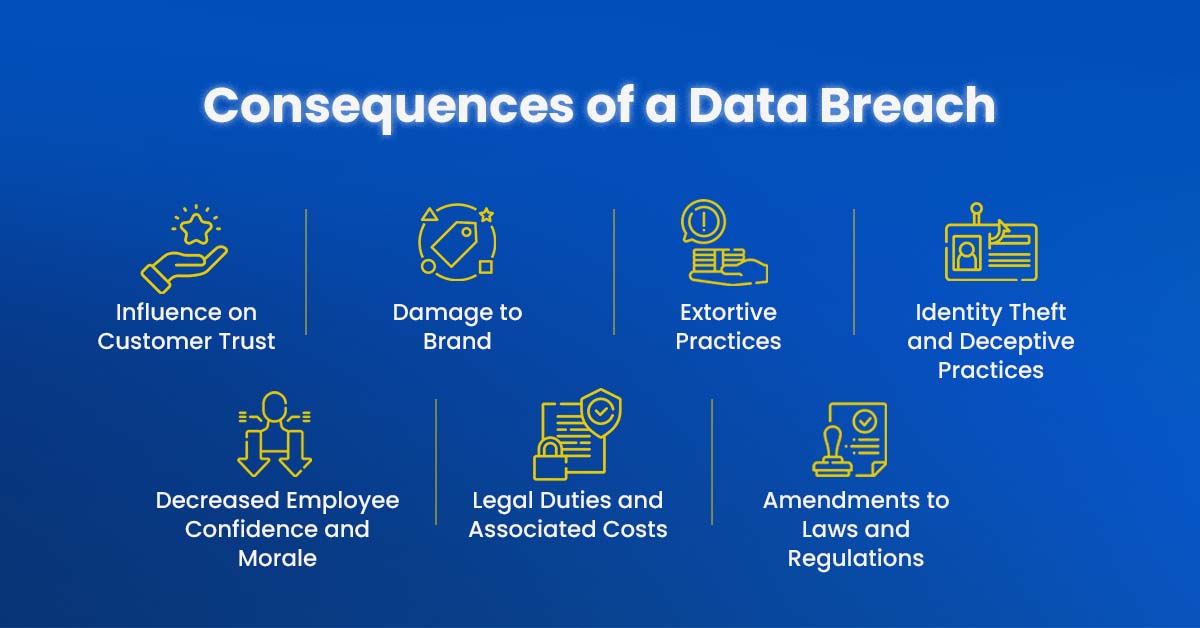
8. Influence on Customer Trust: Current customers who feel exposed or vulnerable as a result of a data breach may stop trusting a company, even if their data has not been accessed or compromised. As a result, they might stop assisting the company, which would drive down sales.
9. Damage to Brand: After a data breach, potential clients, customers, and the general public may have a different opinion of a brand. People may associate a particular brand with being risky or unreliable if the appropriate corrective actions are not taken or if a communication campaign fails. The image of a brand may be permanently harmed by this.
10. Decreased Employee Confidence and Morale: The response of the company to a data breach will be based on how the breach is handled, how well they communicate with all parties affected, and how much employee data was compromised. If the procedure has flaws, this may impact the confidence and morale of the staff members and even have an adverse effect on retention.
11. Identity Theft and Deceptive Practices: This is a natural result of a data breach because the majority of the information that attracts cybercriminals is directly connected to the capacity to commit identity theft and fraud. Identity theft may occasionally become public soon after a breach. Others might take weeks or even years to manifest. A lot of harm can be done in the time it takes to detect and contain a data breach brought on by compromised or stolen credentials.
12. Extortive Practices: A data breach may also involve ransomware. Cybercriminals encrypt data using ransomware, then demand a ransom to decrypt the data. In many cases, businesses that pay the ransom are unable to maintain data resilience and don’t get all of their data back in the end.
13. Legal Duties and Associated Costs: Legalities associated with damages are one cost of a data breach. Another is the potential cost of hiring legal counsel for an organization. A business may be required to follow certain legal procedures to maintain compliance and reduce liability after a breach, including implementing managed security services, notifying affected stakeholders, and investigating the breach.
14. Amendments to Laws and Regulations: A significant enough data breach could prompt regulatory bodies to take more drastic action. Businesses may need to follow new regulations regarding notification, cyber insurance, best practices for data privacy, and more.
In conclusion
The consequences of a data breach on your business can be far-reaching and detrimental. From financial losses and legal liabilities to damaged customer trust and tarnished reputation, the impact can be long-lasting. It is crucial for businesses to understand these potential consequences and take proactive measures to prevent and mitigate data breaches.
By implementing robust cybersecurity measures and managed security services, such as encryption protocols, regular security audits, and employee training programs, you can significantly reduce the risk of a data breach. Additionally, establishing incident response plans and conducting thorough post-breach investigations will help minimize the impact and aid in the recovery process.
Remember, the protection of sensitive data should be a top priority for any organization. Stay vigilant, stay informed, and stay one step ahead of potential threats. In Part 2 of this blog series, we will explore effective strategies and best practices to reduce data breach risk and eliminate its consequences. Together, we can create a safer digital landscape for businesses and their valued stakeholders.
Stay tuned for Part 2: “How to Reduce Data Breach Risk and Eliminate Consequences” for actionable steps and valuable insights. Protecting your business and safeguarding your data is an ongoing effort, but the rewards of a secure and resilient organization are immeasurable.
- 6 Ways AI Reinvents the Security Landscape - January 9, 2024
- Top 6 Current Cybersecurity Trends For 2024 - January 9, 2024
- What Have We Learned from The Recent Cybersecurity Incidents? - January 3, 2024

