Proactive Defense: 7 Critical Measures for Minimizing Risks with Threat Hunting

Threat hunting is the process of aggressively searching for malware or intruders on your network. Since visibility into an organization’s network, endpoint, and application activities can all be signs of an attack, using a security information and event management (SIEM) system to conduct threat hunting is the widely acknowledged method.
SIEM solutions gather log data from a variety of sources, such as servers, firewalls, security programmes, antivirus (AV), and more, centrally. The security mindset of assuming compromise enables security organizations to develop and address the growing number of threats in today’s environment.
Threat hunting is more crucial than ever as hackers develop and discover new ways to access organizations’ internal IT systems.
About 80% of threats can be stopped by the majority of security technologies, yet 20% still go unreported. These lingering dangers are probably much more capable of wreaking havoc. This problem highlights the importance of automated threat hunting because it drastically shortens the time between intrusion and detection.
Every threat search should begin with a threat hunting hypothesis, which is a claim about a strategy or method that applies to your company. The hypothesis should be testable and capable of yielding either a true or false conclusion. Use these seven sorts of hunts to find suspicious irregularities suggestive of threat activity once a threat-hunting hypothesis is prepared:
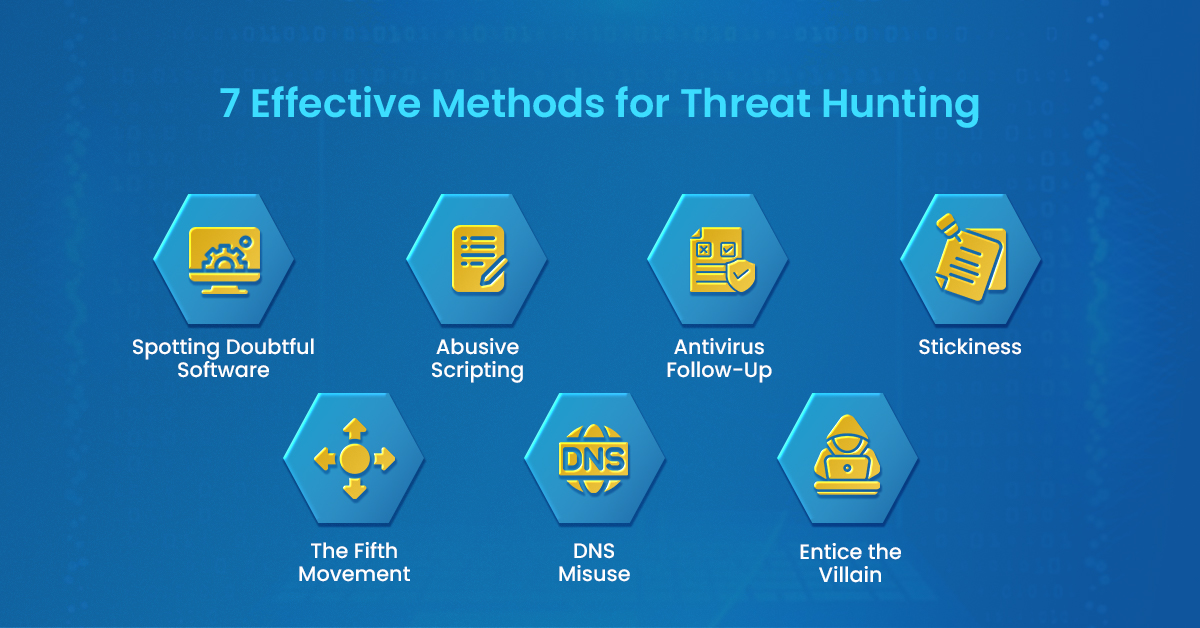
1. Spotting Doubtful Software
Malware that has been installed locally is used by attackers for a number of objectives, including data exfiltration, automation, control, and persistence. However, in order for an attacker to utilize malware, it needs to be running on the endpoint as a process. In order to identify potential attacks, you might look for software that is running on endpoints that is odd.
The process name or the process hash are two approaches to recognize dubious applications. Your SIEM system may be able to receive the log data from your endpoint detection and response (EDR) solution, which would increase your chances of finding problematic applications.
There are two ways to identify questionable applications: the process name or the process hash. You might be able to locate troublesome applications more easily if your SIEM system can get the log data from your endpoint detection and response (EDR) solution.
The process name or the process hash are the two ways to recognize dubious programmes. If your SIEM system is able to access the log data from your endpoint detection and response (EDR) solution, you might be able to identify problematic applications more quickly.
2. Abusive Scripting
Attackers who want to remain undetected often avoid introducing new practices that would alert IT to their presence. Instead, they employ Windows Scripting Host and PowerShell, two scripting languages that are already present on the endpoint.
The simplest danger search involves keeping a look out for scripting engine executions. The CScript, WScript, and PowerShell processes all signal the start of a script. To provide this visibility, more Sysmon, PowerShell operational, and command line parameter logging will probably be required.
3. Antivirus Follow-Up
Using antivirus data throughout your entire organization will help you more accurately determine whether and where malware is spreading throughout your environment. Think of antivirus log data as a potential post-threat intelligence source that can help you find any potential elevated privilege or network segmentation concerns in your environment.
4. Stickiness
As soon as an attacker gets some degree of control over an endpoint, they want to maintain that control even if the endpoint is rebooted, the user logs off, or a malicious process is stopped. Attackers use well-known methods for launching apps to make sure that the malicious code that gives them control starts each and every time the system boots up or a user signs on.
The foundation for monitoring may consist of a baseline of users, processes, and often modified registry keys; however, you may wish to keep a watch on the pertinent keys and provide as much detail as possible on pertinent changes.
5. The Fifth Movement
A hacker’s next move is to move from endpoint to endpoint on the network until they find the target system that contains crucial data.
Odd user or endpoint login combinations and unusual network connections between computers are early warning signs that a threat actor is attempting to move laterally within the network. Monitoring privileged accounts for unusual activity or any hint that they may have been compromised is essential.
6. DNS Misuse
Endpoints should only use DNS requests of the appropriate size to connect with the defined DNS servers. Monitoring for changes to the hosts file or DNS configuration, incredibly high DNS traffic originating from a single endpoint (which suggests data being smuggled through port 53), and DNS rebinding requests are just a few ways to keep a look out for DNS abuse.
7. Entice the villain
The concept of a honeypot is expanded by baiting an attacker to include accounts, files, shares, systems, and even networks as a way to identify attacks without endangering your production environment.
Theoretically, you choose the components of the environment you wish to mimic, establish a virtual environment to act as the honeypot, and then make that environment accessible by leaving open ports that are weak points for attacks, employing simple passwords, and generally making it more inviting to attackers.
Conclusion
Partnering with ESDS for threat hunting can be instrumental in strengthening your organization’s security posture. With our advanced threat intelligence capabilities, experienced threat hunting team, and state-of-the-art Security Operations Center (SOC), ESDS provides a comprehensive suite of services to support your threat hunting initiatives. By leveraging advanced analytics, machine learning, and continuous monitoring, ESDS helps organizations proactively identify and respond to potential threats, minimizing risks and enhancing overall cybersecurity. Furthermore, ESDS’s incident response expertise ensures swift remediation in the event of a security incident, along with post-incident analysis to prevent future occurrences. With ESDS as your trusted cybersecurity partner, you can confidently navigate the complex threat landscape and stay one step ahead of malicious actors.
- Why does your business need Endpoint Detection and Response (EDR)? - May 15, 2024
- Are your business endpoints completely secure? - March 26, 2024
- Is Colocation key to transforming your data center management strategy? - March 22, 2024
