8 Privileged Access Management Best Practices

Failing to manage privileged accounts, a mistake 65% of organizations make, can lead to serious security breaches, regulatory fines, customer backlash, and lasting damage to reputation. In severe cases, it can lead to business closure; a study revealed that 60% of SMBs shut down within six months of a cyber-attack. As security and risk management professionals understand, getting end users and stakeholders to grasp this can be tough. The critical aspect of privileged access management (PAM) isn’t just about identity or management; it’s privileged.
Overview of Privileged Access Management Needs
The current pandemic-driven remote work setups can increase risks. 20 percent of employees report experiencing identity theft, which causes 60 percent of their financial stress. Also, nearly a quarter of fraud victims faced unreimbursed personal expenses, a 3x increase compared to previous years.
34% of data breaches involve an insider threat, often through compromised privileged accounts. PAM safeguards against malicious insiders by enforcing access controls and monitoring privileged user activity.
After gaining initial access, attackers often leverage compromised privileged accounts to move laterally within a network, escalating privileges and expanding their reach. PAM solutions can restrict lateral movement by limiting privileged access.
Privileged Access Management Best Practices
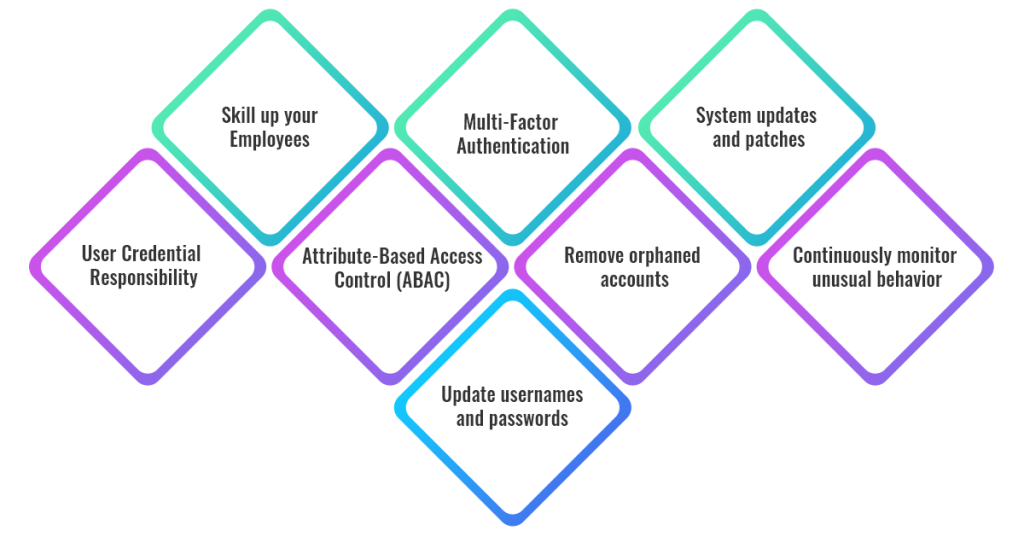
1) Hold users responsible for their credentials.
74% of data breaches start with privileged credential abuse.
Let’s face it: shared credentials are common but risky, especially for privileged accounts. While eliminating sharing might not be realistic, we can significantly reduce the risk by implementing a Privileged Access Management (PAM) process. It assigns individual accountability for credential use, ensuring everyone understands they’re responsible for actions taken under their identity.
2) Attribute-based Access Control (ABAC)
Imagine a more sophisticated way to control access to sensitive data, network infrastructure, and IT resources. Attribute-Based Access Control (ABAC) goes beyond traditional roles. It takes into account actions (read, write, copy, delete), the environment (device, location), and even the user’s specific attributes (department, project) to create a more granular and secure access system. It’s a multi-layered security wall, only allowing authorized users with the right intentions to access specific resources at the right time.
3) Multi-Factor Authentication: The Extra Layer of Security
Cybersecurity thrives on a principle: “Never trust, always verify.” Even when privileged users log in with their credentials, adding an extra layer of verification is wise. This is where Multi-Factor Authentication (MFA) comes in. MFA requires a second step beyond a username and password, such as a code sent to your phone or a fingerprint scan. It’s a format of additional checks to ensure the user is truly who they claim to be before granting access to critical data.
4) Continuously monitor unusual behavior on privileged accounts.
Continuously monitor abnormal behavior on privileged accounts. Session recording helps security teams in handling numerous privileged sessions. Rather than manually reviewing lengthy recordings, Privileged Access Management solutions can analyze footage and establish a standard for user behavior. Any deviation from this standard triggers an alert for security teams, promoting the prioritization and monitoring of unusual actions.
(5) Update default usernames and passwords.
Change default usernames and passwords to mitigate risk. Default credentials pose a significant threat, making them easy targets for cybercriminals. System, device, and application configurations often have simple, publicly known passwords. These passwords are uniform across systems from the same vendor or product line and lack a user interface for management. Initially intended for installation and testing, you must change default passwords before deploying systems in production environments.
(6) Remove orphaned accounts
Orphaned accounts are perfect targets for malicious actors since they lack ownership. Bad actors get the keys to the kingdom through orphaned accounts with privileges. You should consider every identity in your environment when evaluating privileged accounts. Take action to place accounts under governance, assign an owner, or delete accounts you are not accountable for and cannot determine their origin or who is in charge.
(7) Close the gap in security skills among Employees
70% of cybersecurity professionals report the cybersecurity skills shortage impacts their organizations. PAM solutions can automate tasks and streamline workflows, making existing security teams more efficient.
Employees can be your biggest vulnerability regarding effective access management because phishing scams and credential stuffing are too common. Highlight the value of multi-factor authentication and strong passwords to them, and demonstrate how their actions might affect the organization’s overall security. Organize regular training sessions to guarantee that employees understand their roles and know how to manage privileged accounts safely.
(8) System updates and patches
Software vulnerabilities are the entry point to the essential infrastructure in your organization. Maintaining your operating systems, apps, and firmware up to date with the newest security updates will help you stay one step ahead of attackers and defend against potential threats.
The Bottom Line
Every organization’s safety depends heavily on privileged access management tools, which are essential in defending its critical systems from internal and external threats brought on by incorrect use of admin rights. However, mismanaged privileged access management can become a serious issue and significantly raise an organization’s risk. Read the guide to the PAM solution for a better approach to securing your organization.
By implementing these measures, we can create a culture of shared responsibility and build a more secure environment for everyone. It’s a win-win: ESDS empowers users while significantly reducing the risk of unauthorized access and potential breaches.
- Achieving Secure, Reliable Compliance with India’s Data Sovereignty Mandates - November 17, 2025
- Implementing GPU workloads in critical government application - November 12, 2025
- Why the BFSI Industry Needs GPUaaS Now - October 31, 2025

