How safe is your website from web-based threats?
In 2013, many big companies lost money & reputation because of hacking & cyber attacks. The vulnerabilities present in the website or web apps are act as back doors for hackers. There are some common threats that may affect your website. Lets see the main threats to web systems one by one.
SQL Injection:
SQL injection is one of the technique used by hacker in which SQL queries are inserted into input fields for fetching information from databases. In this technique hacker inject different SQL statements into input data field and try to read sensitive information from database. If hacker succeed in getting database credentials then he can perform administrative operations on database such as deleting the database (DROP TABLE) or making modifications in data.
e.g. Your website has ‘Contact us’ form and it takes information from user. In this contact us form the input fields like Name, Address etc are vulnerable to SQL injection. If application programmer has done proper input validations then your database is safe else hacker can compromise the database and he can expose sensitive information.
Remote File Inclusion (RFI):
Remote File Inclusion attacks are executed to target the application servers that host the website & web application. If your website is vulnerable to RFI then attacker can upload malicious scripts/file on your application server through your website. Attacker can grant access to the server and do anything with your website. The RFI threat has huge damage potential through which attacker can steal the stored data or he can hijack whole hosting server.
e.g. Your website have provision for uploading image/doc file. Through the ‘upload file’ field attacker can upload malicious script like shell script. Using the uploaded script attacker can get high privileged access to website.
Again poor field validation checks are the root cause of this RFI.
Malware :
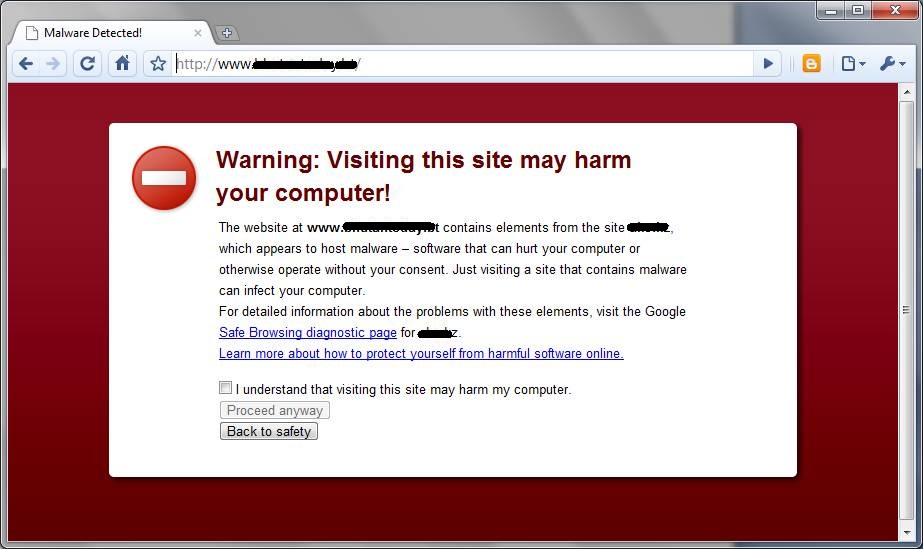
Malware is a malicious software program designed to damage the application system or to steal information for third party’s benefit. The most common types of malwares are worms, Trojans Horse, viruses, worms, spyware etc. Generally hackers inserts malicious links/softwares like invisible iframes, free tools and force users to automatically download malware software without their prior knowledge. Malware can be designed to monitor keyboard strokes through which hacker can steal the passwords of financial transactions. Such malware affected websites becomes blacklisted for hosting malicious content. You might have gone through the browser giving warning if the site is affected by malware.

Cross Site Scripting (XSS) :
In XSS, the hacker inject malicious script(e.g. JavaScript, VBScript ,HTML, flash) into website. Using this script hacker can steal browser cookies and browser cookies may contain sensitive information of website user.
Cross site scripts has potential to deface the website, hijack website user’s session.
Directory traversal
Directory traversal allows hackers to access files in a directory using web browser. In this attacker tries to access restricted Web server files which are present outside of the server’s root directory.
The losses caused by above web threats are huge. Data centres and other stakes used for website hosting need to protected from all types of threats. Modern web sites & web apps are complex and it is not feasible to manually go through each line of code & scan for various threats. Information security professionals recommends use of automated application vulnerability scanner to identify potential security vulnerabilities & threats in the web portal. These scanners crawl through your website & report the security flaws in your website/web application. Using the scan report you can easily fix the vulnerabilities present in your web site & you can eliminate the risk of online reputation loss.
Resources:
- Achieving Secure, Reliable Compliance with India’s Data Sovereignty Mandates - November 17, 2025
- Implementing GPU workloads in critical government application - November 12, 2025
- Why the BFSI Industry Needs GPUaaS Now - October 31, 2025